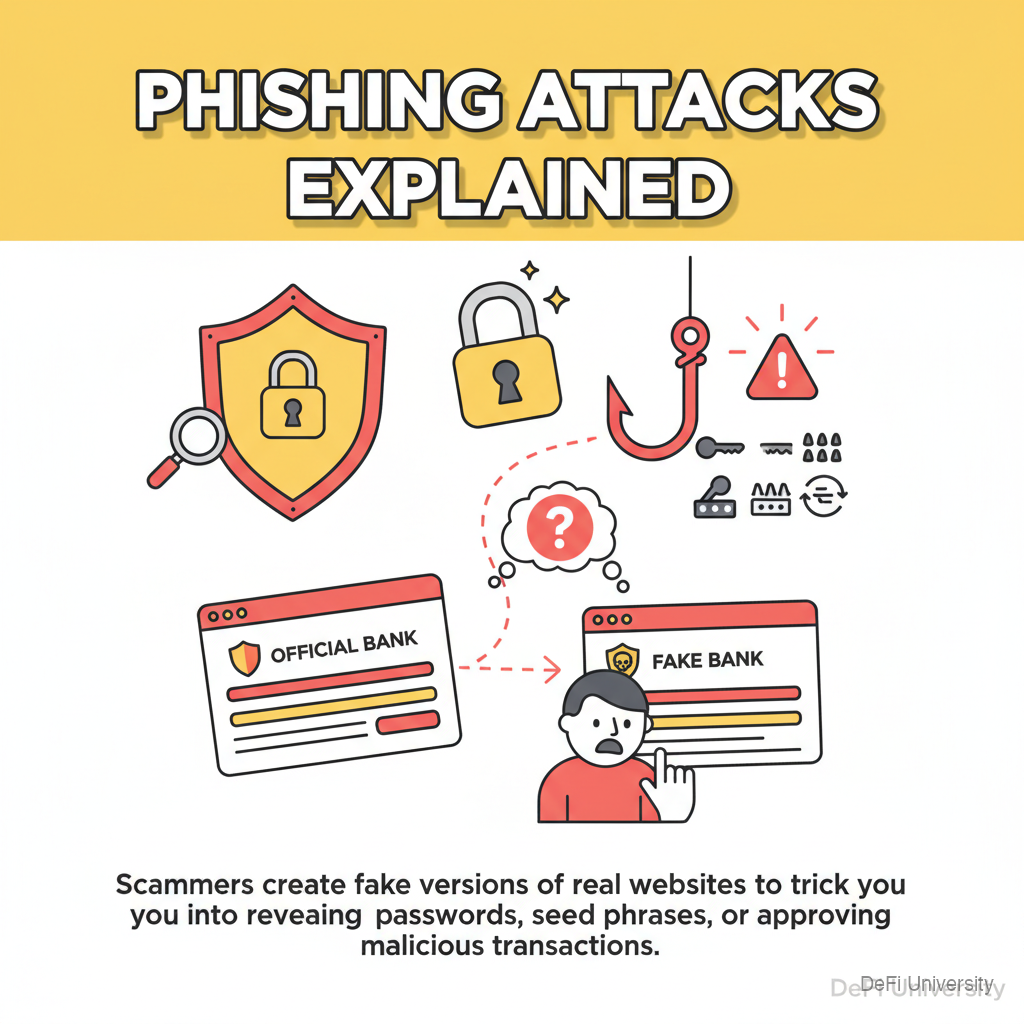
Lesson 1: Phishing Attacks Explained
🎧 Lesson Podcast
🎬 Video Overview
Lesson 1: Phishing Attacks Explained
The Fake Store with a Real Logo
Common Phishing Methods

Fake Websites
Fake Emails
Fake Social Media DMs
Malicious Browser Extensions
Fake Mobile Apps
How to Spot Phishing
What Phishing Sites Ask For
Real Examples of Phishing
Key Takeaways
Last updated